For organizations operating within the defense industrial base, cybersecurity compliance is no longer a policy discussion it is a systems architecture requirement. The U.S. Department of Defense works with more than 220,000 companies across the Defense Industrial Base (DIB), making supply chain cybersecurity a national priority and expanding contractors’ responsibilities for handling sensitive data. Any company that stores, processes, or transmits Controlled Unclassified Information (CUI) must comply with NIST SP 800-171. The most effective way to achieve this is not by hardening an entire enterprise network, but by engineering a dedicated CUI enclave.
A CUI enclave is not simply a secure folder or restricted server. It is a deliberately segmented computing environment designed to isolate sensitive workloads, enforce strict identity controls, and centralize monitoring. When implemented correctly, it transforms compliance from a reactive documentation exercise into a structured, software-driven security strategy.
Table of contents
CUI as an Architectural Risk
Controlled Unclassified Information is sensitive federal information, including defense specifications, technical schematics, contract data, export-controlled data, and certain types of personally identifiable information. While not classified, it does have regulatory protection requirements per DFARS and associated DoD directives.
As soon as CUI touches a general-purpose corporate network, the compliance boundary from a technical perspective widens. Auditing scope can encompass every connected system, user account, and endpoint. This greatly expands risk exposure, infrastructure complexity and audit costs.
That scope, by design, is restricted to a CUI enclave. Instead of trying to secure everything, organizations only secure what touches CUI.
NIST SP 800-171 as a Systems Framework
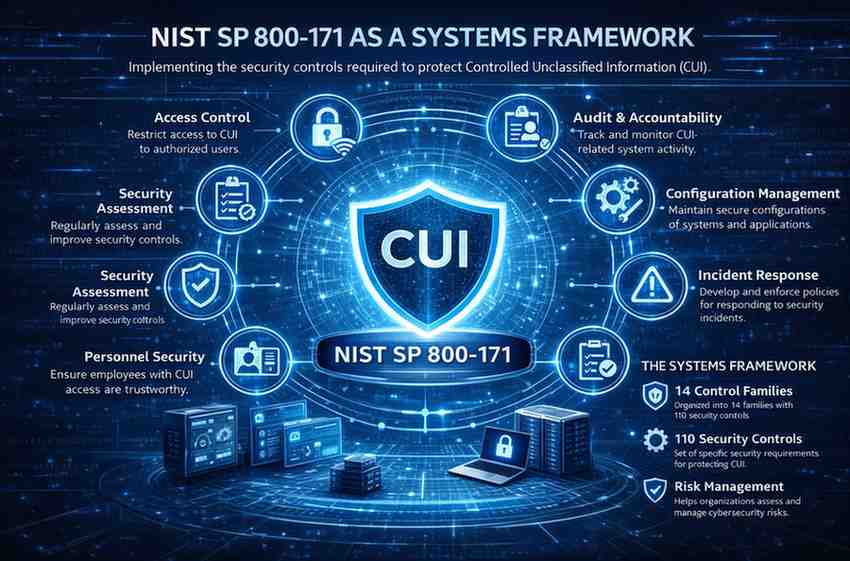
NIST 800-171, developed by the National Institute of Standards and Technology (NIST), focuses on safeguarding Controlled Unclassified Information (CUI) in non-federal systems. Here is a simplified breakdown of its key components:
These controls directly influence infrastructure decisions. Identity architecture must support identity authentication and least-privilege access. Network segmentation must prevent unauthorized lateral movement. Logging systems must provide traceable and immutable audit records. Configuration baselines must be enforced consistently across systems.
Designing a Software-Defined CUI Enclave
Organizations typically build modern CUI enclaves in highly secure cloud environments such as Azure Government or AWS GovCloud. They design the enclave as a logically isolated tenant, subscription, or account with dedicated networking boundaries.
Identity becomes the true perimeter. Conditional access policies, hardware-backed multi-factor authentication, and privileged access management ensure that only authorized users who can establish a secure connection to managed devices can access enclave resources. This fits seamlessly into zero-trust security, where nothing can be trusted automatically, whether within or outside the network.
Endpoint control is equally important. Managed devices with full-disk encryption, endpoint detection and response tools, and centralized policy enforcement help mitigate data exfiltration risk and reduce insider threats. To further isolate sensitive workloads within the enclave, many organizations deploy virtual desktop infrastructure (VDI).
Continuous Monitoring and Audit Readiness
NIST 800-171 compliance is not a one-time certification. It requires continuous monitoring and documented evidence of control effectiveness.
A mature CUI enclave integrates centralized logging into a security information and event management (SIEM) platform. The system records and retains authentication events, configuration changes, access attempts, and administrative actions in accordance with policy. Security teams run vulnerability scanning tools regularly and track remediation workflows through ticketing systems.
This level of visibility ensures that organizations can produce evidence quickly during a CMMC Level 2 assessment. Instead of scrambling to reconstruct logs or policies, they can demonstrate continuous enforcement of controls.
CMMC 2.0 and Enclave Alignment
Organizations that work with CUI must satisfy Level 2 requirements under CMMC 2.0, which are directly mapped to NIST SP 800-171. A clearly defined enclave allows auditors to limit their assessment scope to the systems in the CUI boundary.
It creates a clear delineation, which helps avoid ambiguity in the System Security Plan and also minimizes the scope of assets that are subject to review.
Put differently, if you have a well-designed enclave, it reduces technical and procedural friction significantly.
Cost and Operational Strategy
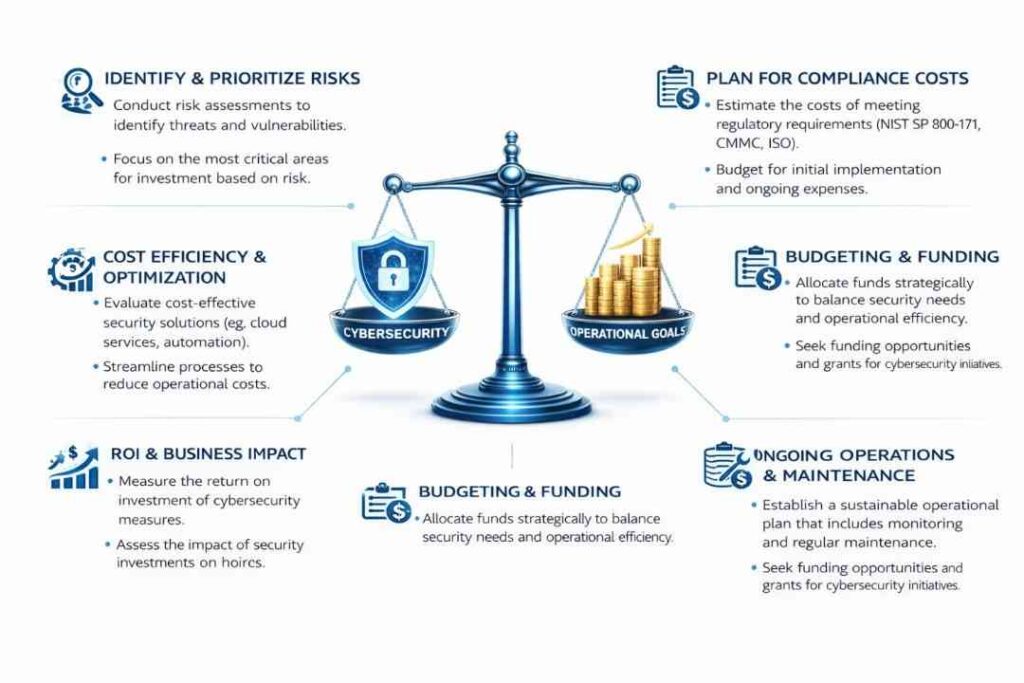
Retrofitting compliance across an entire enterprise environment is often cost-prohibitive. Time and capital are consumed expanding monitoring tools, reconfiguring identity systems, rewriting policy, and auditing legacy infrastructure.
A CUI enclave encloses those requirements within a specific boundary. Infrastructure investments remain focused. There is centralized logging and monitoring. Reporting is focused on enclave systems, not the entire organization.
This is not just a more secure option it’s also a financial strategy. By focusing on reducing compliance surface area, you help organizations lower their long-term operational overhead.
Implementation Approaches
Some organizations build and manage their enclave internally, leveraging experienced security architects and cloud engineers. This approach offers flexibility but requires sustained expertise and ongoing compliance management.
Others leverage specialized compliance-focused cloud platforms that provide pre-architected environments aligned with NIST SP 800-171 controls. Providers such as Cuick Trac, Cleared Systems, and Aunalytics offer structured enclave environments designed to help defense contractors define scope and accelerate compliance readiness.
Regardless of approach, the defining factor is architectural intent. Compliance must be engineered, not improvised.
Final Perspective
The best way to think about NIST SP 800–171 compliance is as a software architecture problem. Orgs that view it as a documentation exercise often grapple with scope creep, many more audits, and increased technical debt. Those that build a purpose-built CUI enclave from the get-go establish an environment that is defensible, scalable and audit-ready.
A well-engineered enclave isolates risk, enforces identity-driven security, centralizes monitoring, and simplifies certification under CMMC 2.0. More importantly, it transforms regulatory obligation into structured cybersecurity maturity.
In an environment where supply chain security is under constant scrutiny, that architectural advantage becomes a competitive one.