Threat intelligence is constantly discussed, yet understood unevenly. Most organisations say they use it. But very few can explain what kind they rely on, where it comes from, or how it actually shapes decisions on a random afternoon when alerts start stacking up.
The stakes are real. According to IBM’s Cost of a Data Breach Report, the global average breach now costs $4.45 million, with organisations taking 204 days to detect and 73 days to contain an incident. Nearly nine months of exposure.
The phrase types of threat intelligence gets thrown around as if it were a neat taxonomy. In practice, it is messier. The boundaries blur. The value shifts depending on who is reading it and why. Some intelligence lands well. Some just fill dashboards.
This blog unpacks the main types of threat intelligence. No frameworks for the sake of frameworks. Just how these intelligence types show up in real security operations.
Table of contents
What Threat Intelligence Really Looks Like in Use
Before breaking it down, it is worth grounding this in reality.
Threat intelligence is not a feed. It is not a PDF. It’s not a weekly email with red and amber boxes. It is context applied to risk. When it works, it shortens decision time. When it does not, it becomes noise with a price tag.
Different teams consume different intelligence. A SOC analyst needs something very different from a board-level risk owner. Confusion usually starts when the same output is pushed to everyone.
That is why understanding the types of Cyber Threat Analysis matters more than collecting more of it.
The Core Types of Threat Intelligence
- Strategic Threat Intelligence
Strategic intelligence sits at the highest level. It looks outward rather than inward. The focus is on long-term trends, adversary intent, geopolitical factors, and industry-specific risk.
This is the intelligence that helps answer questions such as whether a particular sector is becoming more attractive to ransomware groups or how regulatory pressure might shift attacker behaviour over the next year.
It is written for executives, risk committees and anyone shaping security investment. It is not designed to trigger alerts or block traffic.
When strategic intelligence fails, it is usually because it becomes abstract. Too many words. Too little relevance. The best examples are grounded in what the organisation actually does, where it operates, and what would hurt most if disrupted.
- Tactical Threat Intelligence
Tactical intelligence sits closer to operations but still above the keyboard level.
It focuses on adversary tactics, techniques, and procedures. How attackers gain access. How do they move laterally? How they persist. This is where frameworks like MITRE ATT&CK quietly influence thinking, even if nobody mentions them by name.
This intelligence is used by detection engineers, threat hunters, and incident responders. It informs playbooks, detection logic and defensive priorities.
The risk with tactical intelligence is overgeneralisation. Not every technique matters equally to every environment. Good tactical intelligence filters ruthlessly. It says what is likely, not what is possible.
- Operational Threat Intelligence
Operational intelligence is time-sensitive and situational. It is often tied to active campaigns or emerging threats.
This might include intelligence on a new phishing infrastructure being spun up, a ransomware affiliate shifting tooling or a surge in credential harvesting targeting a specific technology.
It tends to be shared quickly and informally. Chat messages. Short reports. Direct briefings. When used well, it sharpens response during incidents or heightened threat periods.
Operational intelligence loses value fast. Old intelligence in this category can be worse than useless. It can create false confidence or unnecessary panic.
- Technical Threat Intelligence
Technical intelligence is the most concrete and the most misunderstood.
It includes indicators such as IP addresses, domains, file hashes, URLs, and sometimes signatures. These are the pieces most commonly automated into tools.
They are also the easiest to misuse.
Indicators without context decay rapidly. Attackers rotate infrastructure. Hashes change. Blocking yesterday’s command-and-control server rarely stops tomorrow’s breach.
Technical intelligence works best when it is tightly coupled with tactical and operational context. On its own, it is brittle.
Seeing The Relationship Between the Types
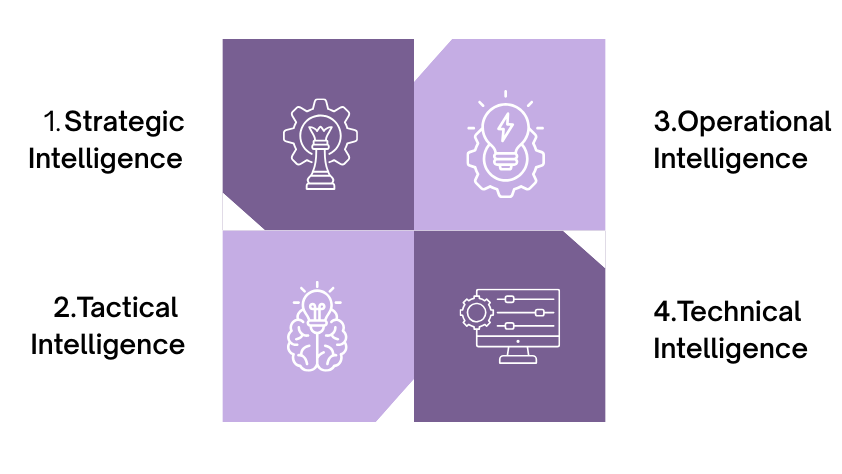
Understanding the types of threat intelligence is easier when you see how they stack and support one another. They are not silos. They are layers:
- Strategic intelligence sets direction and priorities
- Tactical intelligence shapes defensive design and detection
- Operational intelligence responds to live threats and campaigns
- Technical intelligence feeds controls and tools with specific data
When organisations struggle with threat intelligence, it is often because they invest heavily in one layer while ignoring the others. Buying more feeds will not fix a lack of strategic clarity. Writing glossy reports will not help a SOC drowning in alerts.
Balance matters more than volume.
Why Organisations Get Threat Intelligence Wrong
One common mistake is assuming that more intelligence equals better security. It rarely does.
Another is pushing the same intelligence to every audience. Executives do not need IP addresses. Analysts do not need geopolitical essays during an incident.
There is also a tendency to treat cyber threats as a product rather than a capability. Something to subscribe to rather than something to integrate, question, and adapt.
The most mature teams treat intelligence as a conversation. Analysts feed observations back into intelligence requirements. Leadership adjusts priorities based on what the data is actually showing, not what looked good in a quarterly report.
Making Threat Intelligence Usable
Usability is the quiet differentiator.
Good threat intelligence arrives when it is needed. It is framed in language the reader understands. It links clearly to decisions the organisation can make.
This often means saying less, not more. It means discarding intelligence that does not apply. It means accepting that some intelligence is valuable only to a small group, and that is fine.
Threat intelligence is not about predicting the future. It is about reducing uncertainty just enough to act.
Conclusion
Understanding the types of threat intelligence is not an academic exercise. It shapes how organisations invest, how teams operate, and how quickly they respond when something goes wrong.
Strategic, tactical, operational, and technical intelligence all have a role. None of them is sufficient on its own. The real value lies in their alignment with the organisation’s risk, technology, and people.
This is where many security programmes stall. Not because they lack data, but because they lack integration and judgment. CyberNX can help you bring structure to this complexity by providing a comprehensive threat intelligence feed. Plus, they have access to one of the industry’s largest repositories of threat intelligence, with historical data and patterns to contextualize current threats. They also provide real-time insights, integrated security tools, and a proactive defence approach.
Threat intelligence should sharpen thinking, not overwhelm it. When it does, it earns its place at the table.











